

Question : 1
We __________ our friend’s birthday and we ________ how to make it up to him.
Completely forgot --- don’t just know
Forgot completely --- don’t just know
Completely forgot --- just don’t know
Forgot completely --- just don’t know
Correct Answer : C
Question Type : MCQ
Max Marks : 1
Negative Marks : 0.33
Question : 2
Choose the statement where underlined word is used correctly.
The industrialist had a personnel jet.
I write my experience in my personnel diary.
All personnel are being given the day off.
Being religious is a personnel aspect.
Correct Answer : C
Question Type : MCQ
Max Marks : 1
Negative Marks : 0.33
Question : 3
A generic term that includes various items of clothing such as a skirt, a pair of trousers and a shirt is
fabric
textile
fibre
apparel
Correct Answer : D
Question Type : MCQ
Max Marks : 1
Negative Marks : 0.33
Question : 4
Based on the given statements, select the most appropriate option to solve the given question.
What will be the total weight of 10 poles each of same weight?
Statements:
(I) One fourth of the weight of a pole is 5 kg
(II) The total weight of these poles is 160 kg more
than the total weight of two poles.
Statement II alone is not sufficient.
Statement II alone is not sufficient.
Either I or II alone is sufficient.
Both statements I and II together are not sufficient.
Correct Answer : C
Question Type : MCQ
Max Marks : 1
Negative Marks : 0.33
Question : 5
Consider a function \(f(x) = 1 – |x| on –1 ≤ x ≤ 1\). The value of \(x\) at which the function attains a maximum and the maximum value of the function are:
0, –1
–1, 0
0, 1
–1, 2
Correct Answer : C
Question Type : MCQ
Max Marks : 1
Negative Marks : 0.33
Question : 6
Out of the following four sentences, select the most suitable sentence with respect to grammar and usage:
Since the report lacked needed information, it was of no use to them.
The report was useless to them because there were no needed information in it.
Since the report did not contain the needed information, it was not real useful to them.
Since the report lacked needed information, it would not had been useful to them.
Correct Answer : A
Question Type : MCQ
Max Marks : 2
Negative Marks : 0.67
Question : 7
In a triangle PQR, PS is the angle bisector of ∠ QPR and ∠ QPS = 60°. What is the length of PS?
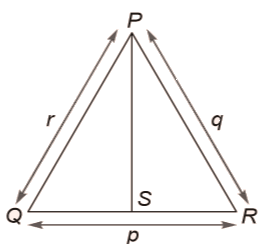
\(\frac {(q + r)} {qr}\)
\(\frac {qr} {q + r}\)
\(\sqrt {(q^2 + r^2)}\)
\(\frac {(q + r)^2} {qr}\)
Correct Answer : B
Question Type : MCQ
Max Marks : 2
Negative Marks : 0.67
Question : 8
If \(p, q, r, s\) are distinct integers such that:
\(f(p, q, r, s) = max (p, q, r, s) \\
g(p, q, r, s) = min (p, q, r, s)\)
\(h(p, q, r, s) \) = remainder of \((p × q) / (r × s)\) if \((p × q) > (r × s)\) OR remainder of \((r × s) / (p × q)\) if \((r × s) > (p × q)\)
Also a function \(fgh (p, q, r, s) = f(p, q, r, s) × g(p, q, r, s) × h(p, q, r, s)\).
Also the same operation are valid with two variable functions of the form \(f(p, q)\).
What is the value of \(fg(h(2, 5, 7, 3), 4, 6, 8)\)?
Correct Answer : 8
Question Type : NAT
Max Marks : 1
Negative Marks : 0
Question : 9
If the list of letters, P, R, S, T, U is an arithmetic sequence, which of the following are also in arithmetic sequence?
I. 2P, 2R, 2S, 2T, 2U
II. P–3, R–3, S–3, T–3, U–3
III. P2, R2, S2, T2, U2
I only
I and II
II and III
I and III
Correct Answer : B
Question Type : MCQ
Max Marks : 2
Negative Marks : 0.67
Question : 10
Four branches of a company are located at M, N, O and P. M is north of N at a distance of 4 km; P is south of O at a distance of 2 km; N is southeast of O by 1 km. What is the distance between M and P in km?
5.34
6.74
28.5
45.49
Correct Answer : A
Question Type : MCQ
Max Marks : 2
Negative Marks : 0.67
Question : 11
Consider the following two statements.
𝑆1: If a candidate is known to be corrupt, then he will not be elected
𝑆2: If a candidate is kind, he will be elected
Which one of the following statements follows from 𝑆1 and 𝑆2 as per sound inference rules of logic?
If a person is known to be corrupt, he is kind
If a person is not known to be corrupt, he is not kind
If a person is kind, he is not known to be corrupt
If a person is not kind, he is not known to be corrupt
Correct Answer : C
Question Type : MCQ
Max Marks : 1
Negative Marks : 0.33
Question : 12
The cardinality of the power set of { 0, 1, 2, …, 10 } is _________.
Correct Answer : 2048
Question Type : NAT
Max Marks : 1
Negative Marks : 0
Question : 13
Let 𝑅 be the relation on the set of positive integers such that 𝑎𝑅𝑏 if and only if 𝑎 and 𝑏 are distinct and have a common divisor other than 1. Which one of the following statements about 𝑅 is true?
𝑅 is symmetric and reflexive but not transitive
𝑅 is reflexive but not symmetric and not transitive
𝑅 is transitive but not reflexive and not symmetric
𝑅 is symmetric but not reflexive and not transitive
Correct Answer : D
Question Type : MCQ
Max Marks : 1
Negative Marks : 0.33
Question : 14
The number of divisors of 2100 is _____ .
Correct Answer : 36
Question Type : NAT
Max Marks : 1
Negative Marks : 0
Question : 15
The larger of the two eigenvalues of the matrix \(\begin{bmatrix} 4 & 5 \\ 2 & 1 \\ \end{bmatrix} \) is _______.
Correct Answer : 6
Question Type : NAT
Max Marks : 1
Negative Marks : 0
Question : 16
An unordered list contains \(n\) distinct elements. The number of comparisons to find an element in this list that is neither maximum nor minimum is
\(Ɵ(n \ log \ n)\)
\(Ɵ(n)\)
\(Ɵ(log \ n)\)
\(Ɵ(1)\)
Correct Answer : D
Question Type : MCQ
Max Marks : 1
Negative Marks : 0.33
Question : 17
The minimum number of JK flip-flops required to construct a synchronous counter with the count sequence (0,0,1,1,2,2,3,3,0,0,…) is __________ .
Correct Answer : 3
Question Type : NAT
Max Marks : 1
Negative Marks : 0
Question : 18
Assume that for a certain processor, a read request takes 50 nanoseconds on a cache miss and 5 nanoseconds on a cache hit. Suppose while running a program, it was observed that 80% of the processor's read requests result in a cache hit. The average read access time in nanoseconds is __________.
Correct Answer : 14
Question Type : NAT
Max Marks : 1
Negative Marks : 0
Question : 19
A computer system implements a 40-bit virtual address, page size of 8 kilobytes, and a 128-entry translation look-aside buffer (TLB) organized into 32 sets each having four ways. Assume that the TLB tag does not store any process id. The minimum length of the TLB tag in bits is _________.
Correct Answer : 22
Question Type : NAT
Max Marks : 1
Negative Marks : 0
Question : 20
Consider the following statements.
I. The complement of every Turing decidable language is Turing decidable
II. There exists some language which is in NP but is not Turing decidable
III. If L is a language in NP, L is Turing decidable
Which of the above statements is/are true?
Only II
Only III
Only I and II
Only I and III
Correct Answer : D
Question Type : MCQ
Max Marks : 1
Negative Marks : 0.33
Question : 21
Consider the following function written in the C programming language.
void foo(char *a)
{
if (*a && *a != ' ')
{
foo(a+1);
putchar(*a);
}
}
The output of the above function on input “ABCD EFGH” is
ABCD EFGH
ABCD
HGFE DCBA
DCBA
Correct Answer : D
Question Type : MCQ
Max Marks : 1
Negative Marks : 0.33
Question : 22
Consider a complete binary tree where the left and the right subtrees of the root are max-heaps. The lower bound for the number of operations to convert the tree to a heap is
\(Ω(log \ 𝑛)\)
\( Ω(𝑛)\)
\(Ω(𝑛 \ log \ 𝑛)\)
\(Ω(𝑛^2)\)
Correct Answer : A
Question Type : MCQ
Max Marks : 1
Negative Marks : 0.33
Question : 23
A binary tree T has 20 leaves. The number of nodes in T having two children is _______.
Correct Answer : 19
Question Type : NAT
Max Marks : 1
Negative Marks : 0
Question : 24
Consider the following C function.
int fun(int n) {
int x=1, k;
if (n==1) return x;
for (k=1; k<n; ++k)
x = x + fun(k) * fun (n-k);
return x;
}
The return value of fun(5) is ________.
Correct Answer : 51
Question Type : NAT
Max Marks : 1
Negative Marks : 0
Question : 25
A software requirements specification (SRS) document should avoid discussing which one of the following?
User interface issues
Non-functional requirements
Design specification
Interfaces with third party software
Correct Answer : C
Question Type : MCQ
Max Marks : 1
Negative Marks : 0.33
Question : 26
Consider two decision problems 𝑄1,𝑄2 such that 𝑄1 reduces in polynomial time to 3-SAT and 3-SAT reduces in polynomial time to 𝑄2. Then which one of the following is consistent with the above statement?
𝑄1 is in NP, 𝑄2 is NP hard.
𝑄2 is in NP, 𝑄1 is NP hard.
Both 𝑄1 and 𝑄2 are in NP .
Both 𝑄1 and 𝑄2 are NP hard.
Correct Answer : A
Question Type : MCQ
Max Marks : 1
Negative Marks : 0.33
Question : 27
Match the following:
|
P. Lexical analysis Q. Parsing R. Register allocation S. Expression evaluation |
1. Graph coloring 2. DFA minimization 3. Post-order traversal 4. Production tree |
P-2, Q-3, R-1, S-4
P-2, Q-1, R-4, S-3
P-2, Q-4, R-1, S-3
P-2, Q-3, R-4, S-1
Correct Answer : C
Question Type : MCQ
Max Marks : 1
Negative Marks : 0.33
Question : 28
In the context of abstract-syntax-tree (AST) and control-flow-graph (CFG), which one of the following is TRUE?
In both AST and CFG, let node \(N_2\) be the successor of node \(N_1\). In the input program, the code corresponding to \(N_2\) is present after the code corresponding to \(N_1\)
For any input program, neither AST nor CFG will contain a cycle
The maximum number of successors of a node in an AST and a CFG depends on the input program
Each node in AST and CFG corresponds to at most one statement in the input program
Correct Answer : C
Question Type : MCQ
Max Marks : 1
Negative Marks : 0.33
Question : 29
Consider the basic COCOMO model where \(E\) is the effort applied in person-months, \(D\) is the development time in chronological months, KLOC is the estimated number of delivered lines of code (in thousands) and 𝑎𝑏 , 𝑏𝑏 , 𝑐𝑏 , 𝑑𝑏 have their usual meanings. The basic COCOMO equations are of the form
\(E=a_b (KLOC) exp(b_b), D=c_b(E) exp(d_b)\)
\(D=a_b (KLOC) exp(b_b), E=c_b(D) exp(d_b)\)
\(E=a_b exp(b_b), D=c_b (KLOC) exp(d_b)\)
\(E=a_b exp(d_b), D=c_b (KLOC) exp(b_b)\)
Correct Answer : A
Question Type : MCQ
Max Marks : 1
Negative Marks : 0.33
Question : 30
A system has 6 identical resources and \(N\) processes competing for them. Each process can request atmost 2 resources. Which one of the following values of \(N\) could lead to a deadlock?
1
2
3
4
Correct Answer : D
Question Type : MCQ
Max Marks : 1
Negative Marks : 0.33
Question : 31
Consider the following transaction involving two bank accounts x and y.
read(x); x := x – 50; write(x); read(y); y := y + 50; write(y)
The constraint that the sum of the accounts x and y should remain constant is that of
Atomicity
Consistency
Isolation
Durability
Correct Answer : B
Question Type : MCQ
Max Marks : 1
Negative Marks : 0.33
Question : 32
With reference to the B+ tree index of order 1 shown below, the minimum number of nodes (including the Root node) that must be fetched in order to satisfy the following query: "Get all records with a search key greater than or equal to 7 and less than 15" is ____________.
Correct Answer : 5
Question Type : NAT
Max Marks : 1
Negative Marks : 0
Question : 33
Identify the correct order in which a server process must invoke the function calls accept, bind, listen, and recv according to UNIX socket API.
listen, accept, bind, recv
bind, listen, accept, recv
bind, accept, listen, recv
accept, listen, bind, recv
Correct Answer : B
Question Type : MCQ
Max Marks : 1
Negative Marks : 0.33
Question : 34
A link has a transmission speed of 106 bits/sec. It uses data packets of size 1000 bytes each. Assume that the acknowledgment has negligible transmission delay, and that its propagation delay is the same as the data propagation delay. Also assume that the processing delays at nodes are negligible. The efficiency of the stop-and-wait protocol in this setup is exactly 25%. The value of the one-way propagation delay (in milliseconds) is ____________.
Correct Answer : 12
Question Type : NAT
Max Marks : 1
Negative Marks : 0
Question : 35
Which one of the following statements is NOT correct about HTTP cookies?
A cookie is a piece of code that has the potential to compromise the security of an Internet user
A cookie gains entry to the user’s work area through an HTTP header
A cookie has an expiry date and time
Cookies can be used to track the browsing pattern of a user at a particular site
Correct Answer : A
Question Type : MCQ
Max Marks : 1
Negative Marks : 0.33
Question : 36
Consider the following routing table at an IP router:
\(\begin{array}{|l|l|l|} \hline \textbf {Network No} & \textbf {Net Mask} & \textbf{Next Hop} \\\hline \text {128.96.170.0} & \text{255.255.254.0} & \text{Interface $0$} \\\hline\text {128.96.168.0} & \text{255.255.254.0} & \text{Interface $1$} \\\hline\text {128.96.166.0} & \text{255.255.254.0} & \text{R$2$}\\\hline \text {128.96.164.0} & \text{255.255.252.0} & \text{R$3$}\\\hline \text {0.0.0.0} & \text{Default} & \text{R$4$}\\\hline \end{array}\)
For each IP address in Group I identify the correct choice of the next hop from Group II using the entries from the routing table above.
|
Group I i) 128.96.171.92 |
Group II a) Interface 0 |
i-a, ii-c, iii-e, iv-d
i-a, ii-d, iii-b, iv-e
i-b, ii-c, iii-d, iv-e
i-b, ii-c, iii-e, iv-d
Correct Answer : A
Question Type : MCQ
Max Marks : 2
Negative Marks : 0.67
Question : 37
Host A sends a UDP datagram containing 8880 bytes of user data to host B over an Ethernet LAN. Ethernet frames may carry data up to 1500 bytes (i.e. MTU=1500 bytes). Size of UDP header is 8 bytes and size of IP header is 20 bytes. There is no option field in IP header. How many total number of IP fragments will be transmitted and what will be the contents of offset field in the last fragment?
6 and 925
6 and 7400
7 and 1110
7 and 8880
Correct Answer : C
Question Type : MCQ
Max Marks : 2
Negative Marks : 0.67
Question : 38
Assume that the bandwidth for a TCP connection is 1048560 bits /sec. Let α be the value of RTT in milliseconds (rounded off to the nearest integer) after which the TCP window scale option is needed. Let β be the maximum possible window size with window scale option. Then the values of α and β are
63 milliseconds, 65535 x 214
63 milliseconds, 65535 x 216
500 milliseconds, 65535 x 214
500 milliseconds, 65535 x 216
Correct Answer : C
Question Type : MCQ
Max Marks : 2
Negative Marks : 0.67
Question : 39
Consider a simple checkpointing protocol and the following set of operations in the log.
(start, T4); (write, T4, \(y\), 2, 3); (start, T1); (commit, T4); (write, T1, \(z\), 5, 7);
(checkpoint);
(start, T2); (write, T2, \(x\), 1, 9); (commit, T2); (start, T3), (write, T3, \(z\), 7, 2);
If a crash happens now and the system tries to recover using both undo and redo operations, what are the contents of the undo list and the redo list?
Undo: T3, T1; Redo: T2
Undo: T3, T1; Redo: T2, T4
Undo: none; Redo: T2, T4, T3, T1
Undo: T3, T1, T4; Redo: T2
Correct Answer : A
Question Type : MCQ
Max Marks : 2
Negative Marks : 0.67
Question : 40
Consider two relations R1(A,B) with the tuples (1,5), (3,7) and R2(A,C) = (1,7), (4,9). Assume that R(A,B,C) is the full natural outer join of R1 and R2. Consider the following tuples of the form (A,B,C): \(a\) = (1,5,\(null\)), \(b\) = (1,\(null\),7), \(c\) = (3, \(null\), 9), \(d\) = (4,7,\(null\)), \(e\) = (1,5,7), \(f\) = (3,7,\(null\)), \(g\) = (4,\(null\),9). Which one of the following statements is correct?
R contains \(a, b, e, f, g\) but not \(c, d\).
R contains all of \(a, b, c, d, e, f, g\).
R contains \(e, f, g\) but not \(a, b\).
R contains \(e\) but not \(f, g\).
Correct Answer : C
Question Type : MCQ
Max Marks : 2
Negative Marks : 0.67
Question : 41
Consider six memory partitions of sizes 200 KB, 400 KB, 600 KB, 500 KB, 300 KB and 250 KB, where KB refers to kilobyte. These partitions need to be allotted to four processes of sizes 357 KB, 210 KB, 468 KB and 491 KB in that order. If the best fit algorithm is used, which partitions are NOT allotted to any process?
200 KB and 300 KB
200 KB and 250 KB
250 KB and 300 KB
300 KB and 400 KB
Correct Answer : A
Question Type : MCQ
Max Marks : 2
Negative Marks : 0.67
Question : 42
Consider a typical disk that rotates at 15000 rotations per minute (RPM) and has a transfer rate of 50×106 bytes/sec. If the average seek time of the disk is twice the average rotational delay and the controller’s transfer time is 10 times the disk transfer time, the average time (in milliseconds) to read or write a 512-byte sector of the disk is _________________.
Correct Answer : 6.1 to 6.2
Question Type : NAT
Max Marks : 2
Negative Marks : 0
Question : 43
A computer system implements 8 kilobyte pages and a 32-bit physical address space. Each page table entry contains a valid bit, a dirty bit, three permission bits, and the translation. If the maximum size of the page table of a process is 24 megabytes, the length of the virtual address supported by the system is _______________ bits.
Correct Answer : 36
Question Type : NAT
Max Marks : 2
Negative Marks : 0
Question : 44
Consider the intermediate code given below.
(1) i=1 (2) j=1 (3) t1 = 5 * i (4) t2 = t1 + j (5) t3 = 4 * t2 (6) t4 = t3 (7) a[t4] = -1 (8) j = j + 1 (9) if j <= 5 goto (3) (10) i = i +1 (11) if i < 5 goto (2)
The number of nodes and edges in the control-flow-graph constructed for the above code, respectively, are
5 and 7
6 and 7
5 and 5
7 and 8
Correct Answer : B
Question Type : MCQ
Max Marks : 2
Negative Marks : 0.67
Question : 45
The number of states in the minimal deterministic finite automaton corresponding to the regular expression (0 + 1)∗(10) is __________.
Correct Answer : 3
Question Type : NAT
Max Marks : 2
Negative Marks : 0
Question : 46
Which of the following languages is/are regular?
\(L_1: \left\{ wxw^R \mid w, x \in \{a, b\} ^* \text{ and } |w|, |x| > 0\right\}, w^R \text{ is the reverse of string } w\)
\(L_2: \left\{ a^nb^m \mid m \neq n \text { and } m, n \geq 0 \right\}\)
\(L_3: \left\{ a^pb^qc^r \mid p, q, r \geq 0 \right\}\)
\(L_1\) and \(L_3\) only
\(L_2\) only
\(L_2\) and \(L_3\) only
\(L_3\) only
Correct Answer : A
Question Type : MCQ
Max Marks : 2
Negative Marks : 0.67
Question : 47
Given below are some algorithms, and some algorithm design paradigms.
| 1. Dijkstra’s Shortest Path 2. Floyd-Warshall algorithm to compute all pairs shortest path 3. Binary search on a sorted array 4. Backtracking search on a graph |
i. Divide and Conquer ii. Dynamic Programming iii. Greedy design iv. Depth-first search v. Breadth-first search |
Match the above algorithms on the left to the corresponding design paradigm they follow.
1-i, 2-iii, 3-i, 4-v.
1-iii, 2-iii, 3-i, 4-v.
1-iii, 2-ii, 3-i, 4-iv.
1-iii, 2-ii, 3-i, 4-v.
Correct Answer : C
Question Type : MCQ
Max Marks : 2
Negative Marks : 0.67
Question : 48
A Young tableau is a 2D array of integers increasing from left to right and from top to bottom. Any unfilled entries are marked with ∞, and hence there cannot be any entry to the right of, or below a ∞. The following Young tableau consists of unique entries.
\(\begin{array}{|l|l|l|l|}\hline \textbf{1} & \text{2}& \text{5} & \text{14} \\\hline \text{3} & \text{4} & \text{6} & \text{23} \\\hline \text{10} & \text{12} & \text{18} & \text{25} \\\hline \text{31} & \text{$\infty$} & \text{$\infty$} & \text{$\infty$} \\\hline \end{array}\)
When an element is removed from a Young tableau, other elements should be moved into its place so that the resulting table is still a Young tableau (unfilled entries may be filled in with a ∞). The minimum number of entries (other than 1) to be shifted, to remove 1 from the given Young tableau is ______________.
Correct Answer : 5
Question Type : NAT
Max Marks : 2
Negative Marks : 0
Question : 49
Suppose you are provided with the following function declaration in the C programming language.
int partition(int a[], int n);
The function treats the first element of \(a\)[ ] as a pivot and rearranges the array so that all elements less than or equal to the pivot is in the left part of the array, and all elements greater than the pivot is in the right part. In addition, it moves the pivot so that the pivot is the last element of the left part. The return value is the number of elements in the left part.
The following partially given function in the C programming language is used to find the \(k^{th}\) smallest element in an array \(a\)[ ] of size \(n\) using the partition function. We assume \(k \leq n\).
int kth_smallest (int a[], int n, int k)
{
int left_end = partition (a, n);
if (left_end+1==k) {
return a[left_end];
}
if (left_end+1 > k) {
return kth_smallest (___________);
} else {
return kth_smallest (___________);
}
}
The missing arguments lists are respectively
(a, left_end, k) and (a+left_end+1, n-left_end-1, k-left_end-1)
(a, left_end, k) and (a, n-left_end-1, k-left_end-1)
(a+left_end+1, n-left_end-1, k-left_end-1) and (a, left_end, k)
(a, n-left_end-1, k-left_end-1) and (a, left_end, k)
Correct Answer : A
Question Type : MCQ
Max Marks : 2
Negative Marks : 0.67
Question : 50
Which one of the following hash functions on integers will distribute keys most uniformly over 10 buckets numbered 0 to 9 for 𝑖𝑖 ranging from 0 to 2020?
\(ℎ(𝑖) = 𝑖^2 \ mod \ 10\)
\(ℎ(𝑖) = 𝑖^3 \ mod \ 10\)
\(ℎ(𝑖) = (11 * 𝑖^2) \ mod \ 10\)
\(ℎ(𝑖) = (12 * 𝑖) \ mod \ 10\)
Correct Answer : B
Question Type : MCQ
Max Marks : 2
Negative Marks : 0.67
Question : 51
The secant method is used to find the root of an equation f(x) = 0. It is started from two distinct estimates xa and xb for the root. It is an iterative procedure involving linear interpolation to a root. The iteration stops if f(xb) is very small and then xb is the solution. The procedure is given below. Observe that there is an expression which is missing and is marked by ?. Which is the suitable expression that is to be put in place of ? so that it follows all steps of the secant method?
Secant
Initialize: xa, xb, ε, N // ε = convergence indicator
fb = f(xb) i = 0
while (i < N and |fb| > ε) do
i = i + 1 // update counter
xt = ? // missing expression for
// intermediate value
xa = xb // reset xa
xb = xt // reset xb
fb = f(xb) // function value at new xb
end while
if |fb| > ε
then // loop is terminated with i = N
write “Non-convergence”
else
write “return xb”
end if
xb – (fb– f(xa)) fb/ (xb – xa)
xa– (fa– f(xa)) fa/ (xb – xa)
xb – (fb – xa) fb/ (xb – fb(xa)
xa – (xb – xa) fa/ (fb – f(xa))
Correct Answer : C
Question Type : MCQ
Max Marks : 2
Negative Marks : 0.67
Question : 52
Consider the C program below.
#include <stdio.h>
int *A, stkTop;
int stkFunc (int opcode, int val)
{
static int size=0, stkTop=0;
switch (opcode) {
case -1: size = val; break;
case 0: if (stkTop < size ) A[stkTop++]=val; break;
default: if (stkTop) return A[--stkTop];
}
return -1;
}
int main()
{
int B[20]; A=B; stkTop = -1;
stkFunc (-1, 10);
stkFunc (0, 5);
stkFunc (0, 10);
printf ("%d\n", stkFunc(1, 0)+ stkFunc(1, 0));
}
The value printed by the above program is __________.
Correct Answer : 15
Question Type : NAT
Max Marks : 2
Negative Marks : 0
Question : 53
Consider the sequence of machine instructions given below:
MUL R5, R0, R1
DIV R6, R2, R3
ADD R7, R5, R6
SUB R8, R7, R4
In the above sequence, R0 to R8 are general purpose registers. In the instructions shown, the first register stores the result of the operation performed on the second and the third registers. This sequence of instructions is to be executed in a pipelined instruction processor with the following 4 stages: (1) Instruction Fetch and Decode (IF), (2) Operand Fetch (OF), (3) Perform Operation (PO) and (4) Write back the result (WB). The IF, OF and WB stages take 1 clock cycle each for any instruction. The PO stage takes 1 clock cycle for ADD or SUB instruction, 3 clock cycles for MUL instruction and 5 clock cycles for DIV instruction. The pipelined processor uses operand forwarding from the PO stage to the OF stage. The number of clock cycles taken for the execution of the above sequence of instructions is ___________.
Correct Answer : 13
Question Type : NAT
Max Marks : 2
Negative Marks : 0
Question : 54
Consider a processor with byte-addressable memory. Assume that all registers, including Program Counter (PC) and Program Status Word (PSW), are of size 2 bytes. A stack in the main memory is implemented from memory location (0100)16 and it grows upward. The stack pointer (SP) points to the top element of the stack. The current value of SP is (016E)16. The CALL instruction is of two words, the first word is the op-code and the second word is the starting address of the subroutine (one word = 2 bytes). The CALL instruction is implemented as follows:
The content of PC just before the fetch of a CALL instruction is (5FA0)16. After execution of the CALL instruction, the value of the stack pointer is
(016A)16
(016C)16
(0170)16
(0172)16
Correct Answer : D
Question Type : MCQ
Max Marks : 2
Negative Marks : 0.67
Question : 55
The number of min-terms after minimizing the following Boolean expression is _________.
[𝐷′ + 𝐴𝐵′ + 𝐴′𝐶 + 𝐴𝐶′𝐷 + 𝐴′𝐶′𝐷]′
Correct Answer : 1
Question Type : NAT
Max Marks : 2
Negative Marks : 0
Question : 56
Let \(𝑓(𝑥) = 𝑥^{−(1/3)}\) and 𝐴 denote the area of the region bounded by \(𝑓(𝑥)\) and the X-axis, when 𝑥 varies from −1 to 1. Which of the following statements is/are TRUE?
I) 𝑓 is continuous in [−1, 1]
II) 𝑓 is not bounded in [−1, 1]
III) 𝐴 is nonzero and finite
II only
III only
II and III only
I, II and III
Correct Answer : C
Question Type : MCQ
Max Marks : 2
Negative Marks : 0.67
Question : 57
Perform the following operations on the matrix \(\begin{bmatrix} 3 & 4 & 45 \\ 7 & 9 & 105 \\ 13 & 2 & 195 \end{bmatrix}\)
(i) Add the third row to the second row
(ii) Subtract the third column from the first column.
The determinant of the resultant matrix is___________.
Correct Answer : 0
Question Type : NAT
Max Marks : 2
Negative Marks : 0
Question : 58
The number of onto functions (surjective functions) from set 𝑋 = {1, 2, 3, 4} to set 𝑌 = {𝑎, 𝑏, 𝑐} is __________.
Correct Answer : 36
Question Type : NAT
Max Marks : 2
Negative Marks : 0
Question : 59
Let 𝑋 and 𝑌 denote the sets containing 2 and 20 distinct objects respectively and 𝐹 denote the set of all possible functions defined from 𝑋 to 𝑌. Let 𝑓 be randomly chosen from 𝐹. The probability of 𝑓 being one-to-one is ________.
Correct Answer : 0.95
Question Type : NAT
Max Marks : 2
Negative Marks : 0
Question : 60
Consider the alphabet ∑ = {0, 1}, the null/empty string 𝜆 and the sets of strings X0, X1, and X2 generated by the corresponding non-terminals of a regular grammar. X0, X1, and X2 are related as follows.
X0 = 1 X1
X1 = 0 X1 + 1 X2
X2 = 0 X1 + {𝜆}
Which one of the following choices precisely represents the strings in X0?
10(0* + (10)*)1
10(0* + (10)*)*1
1(0 + 10)*1
10(0 + 10)*1 + 110(0 + 10)*1
Correct Answer : C
Question Type : MCQ
Max Marks : 2
Negative Marks : 0.67
Question : 61
A graph is self-complementary if it is isomorphic to its complement. For all self-complementary graphs on 𝑛 vertices, 𝑛 is
A multiple of 4
Even
Odd
Congruent to \(0 \ mod \ 4\), or, \(1 \ mod \ 4\).
Correct Answer : D
Question Type : MCQ
Max Marks : 2
Negative Marks : 0.67
Question : 62
In a connected graph, a bridge is an edge whose removal disconnects a graph. Which one of the following statements is true?
A tree has no bridges
A bridge cannot be part of a simple cycle
Every edge of a clique with size ≥ 3 is a bridge (A clique is any complete subgraph of a graph)
A graph with bridges cannot have a cycle
Correct Answer : B
Question Type : MCQ
Max Marks : 2
Negative Marks : 0.67
Question : 63
Which one of the following well formed formulae is a tautology?
\(\forall x \, \exists y \, R(x,y) \, \leftrightarrow \, \exists y \, \forall x \, R(x, y)\)
\(( \forall x \, [\exists y \, R(x,y) \, \rightarrow \, S(x, y)]) \, \rightarrow \, \forall x \, \exists y \, S(x, y)\)
\([ \forall x \, \exists y \, \left( P(x,y) \, \rightarrow \, R(x, y) \right)] \, \leftrightarrow [ \forall x \, \exists y \left(\neg P(x, y) \, \lor R(x, y) \right)]\)
\(\forall x \, \forall y \, P(x,y) \, \rightarrow \, \forall x \, \forall y \, P(y, x)\)
Correct Answer : C
Question Type : MCQ
Max Marks : 2
Negative Marks : 0.67
Question : 64
Which one of the following assertions concerning code inspection and code walkthrough is true?
Code inspection is carried out once the code has been unit tested
Code inspection and code walkthrough are synonyms
Adherence to coding standards is checked during code inspection
Code walkthrough is usually carried out by an independent test team
Correct Answer : C
Question Type : MCQ
Max Marks : 2
Negative Marks : 0.67
Question : 65
A half adder is implemented with XOR and AND gates. A full adder is implemented with two half adders and one OR gate. The propagation delay of an XOR gate is twice that of an AND/OR gate. The propagation delay of an AND/OR gate is 1.2 microseconds. A 4-bit ripple-carry binary adder is implemented by using four full adders. The total propagation time of this 4-bit binary adder in microseconds is____________.
Correct Answer : 19.2
Question Type : NAT
Max Marks : 2
Negative Marks : 0